Secure Phones Series: What makes a phone secure and private?
The ever increasing need for mobile communications equally means ever increasing need for secure and private phones. Businesses, organizations, and agencies all have a use for secure devices creating tremendous demand in the market. The question we often hear is, “What makes a secure device, secure?” This is an important question and Copperhead has direct experience in the market, on the front lines in bleeding-edge secure Android development. To paint a clear picture of what makes a device secure, we need to break down the essential components necessary for that device to be considered secure and private. In light of the quantity of information that is both relevant and required here, we’ll be presenting a 3-part series for each component of a secure phone. These components are the device or hardware, operating system, and user practices. Here is a little of what we have learned.
This post will outline an important and necessary piece of the secure phone solution: the Hardware.
Device Security
The security of a secure phone begins at the manufacturer level. When a device manufacturer is designing a new phone they are presented with options for the hardware to be placed in the device. The System on Chip (SoC) selection, which is the architectural blueprint of the Android device directly impacts the security capacity of that device. After the SoC is the inclusion of a Secure Element such as the Pixel’s Titan M chip. These chips lock down operating system processes inside of a secure hardware container, isolated from potentially malicious processes.
System on Chip: Where it all begins
System on Chip is described by Wikipedia as “an integrated circuit (also known as a "chip") that integrates all or most components of a computer or other electronic system.” The SoC used by a phone, secure or otherwise, determines the hardware capacity of that phone to then include other components. The state of SoC support is reliant on only a few players in the space (Qualcomm, Mediatek, NXP) meaning that there are few options for device manufacturers to choose from. Secure phones absolutely require the latest in SoC versions, as it dictates the Linux kernel version and therefore, the capabilities of the operating system utilizing the SoC. Certainly the older the SoC in a phone is, the less security capabilities the operating system and that device have. The latest iteration of Linux phones in the mobile phone space have this exact problem (see here for an example of a SoC which a unreleased Linux Phone is using). Ensuring that the entire software, and operating system stack are FOSS/OSS enabled may mean that the involved components are not up-to-date or even pass current security specs. Proponents of the Free Software movement may be okay with this trade-off of security for openness: Copperhead is not. An updated System on Chip design helps provide the security blueprint for the device’s hardware.
Linux Kernel on Mobile
Android uses the Linux kernel for interfacing with the hardware on the phone. Older SoCs rely on older Linux kernel versions for both Android and Linux support. Using Linux kernels is a double edged-sword; the development of the Linux kernel is based on what the consensus of importance for inclusion is: Wikipedia states that “As of 2020, the 5.6 release of the Linux kernel had around 33 million lines of code, roughly 14% of the code is part of the "core" (arch, kernel and mm directories) while 60% is drivers.” Thanks to the elevated privileges of drivers they are often the first exploited resource on an endpoint such as a mobile phone. Controlling a driver means near complete control of the device. The addition of more drivers in the Linux kernel opens up more exploitation possibilities, unnecessarily increasing attack surface. Using a stable Long Term Support (LTS) Linux kernel means we can robustly security test and strip away unused drivers. In comparison, using the latest and greatest Linux kernel may actually introduce dangerous new bugs into a deployment. Copperhead has routinely cherry-picked updated Linux security features and included them in stable LTS kernels for CopperheadOS.
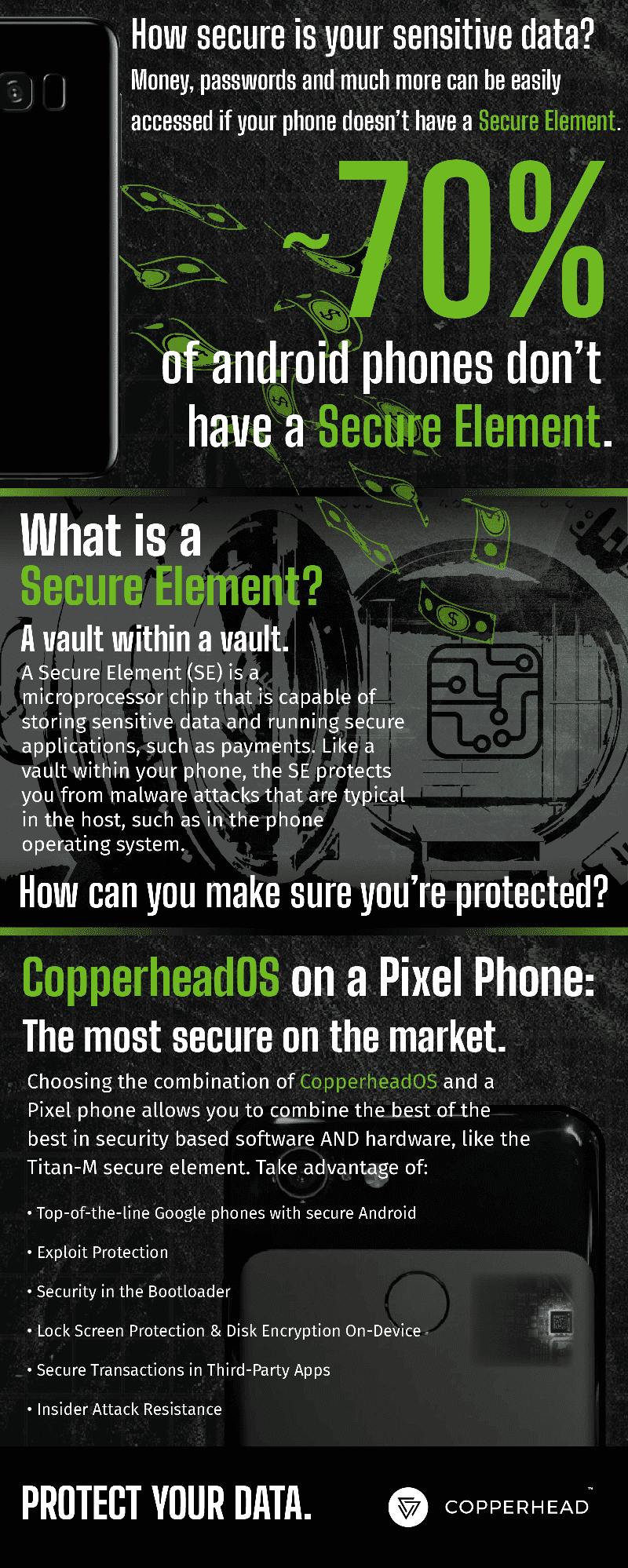
Secure Element
Secure Elements are the quintessential component for a phone to be considered a secure phone. Secure Elements sometimes called a Hardware Security Module (HSM), provide a safe shelter for operations inside of a secluded hardware environment for sensitive processes and verifying the boot chain of a device. In the event that a device is compromised by malware, processes such as bank transactions are still protected from malware on the device through Android’s Protected Confirmation API. Secure Elements provide a tamper-proof outline of the operating system components to verify from, restricting tampering with system integrity or making file changes without authorization. For example malware is often designed to be persistent, to stay on the device after being deleted or even factory reset. Malware that attempts to create persistence cannot lay the groundwork to do so because the Titan M chip verifies the integrity of the device. Malware and malicious operations cannot tamper with Verified Boot, protecting the device security and ensuring a truly secure phone. Android has provided Verified Boot since Android 4.4 and CopperheadOS has utilized this mechanism to protect our customers from since we released CopperheadOS on the Nexus 5X.
While not all Secure Elements are created equally, the security of the Pixel’s Titan M chip is supported by a large bug bounty and organizations such as Project Zero. The Titan M is used in Pixel devices for Verified Boot and supporting the hardware-backed keystore which provides unalterable security services to the OS and applications. Only recently have manufacturers begin including Secure Elements inside of their Android devices, while the Pixel series has had a Secure Element since Pixel 2.
The Titan M chip reigns as the supreme HSM and protects users who want a truly secure phone.
The Most Secure Phone on the market today is the Pixel with CopperheadOS
Not all devices are created equal and although Android phone manufacturers have begun to take the correct steps toward protecting their users, the Google Pixel device remains the most secure Android phone. With a combination of the Titan M HSM, using a robust and secure LTS Linux Kernel, updated patches from Qualcomm/Google, the availability of locking the Pixel bootloader and the inclusion of a secure operating system like CopperheadOS give customers the winning secure solution for mobile communications.