Android Security accelerates against zero-day exploits
The cybersecurity world is an ecosystem of firms and freelancers, all providing critical infrastructure to the modern digital world. One of the key roles in this infrastructure is the penetration tester, also known as the white-hat hacker. These white-hats search out critical security vulnerabilities with the purpose of reporting them to developers. Certain firms have made a business of offering bounties for unknown vulnerabilities, called zero-day exploits.
Exploit vendors target iOS
Since 2015, bounty offerings have been growing to substantial figures with Zerodium leading the charge by offering $1 million US for an iOS zero-day.
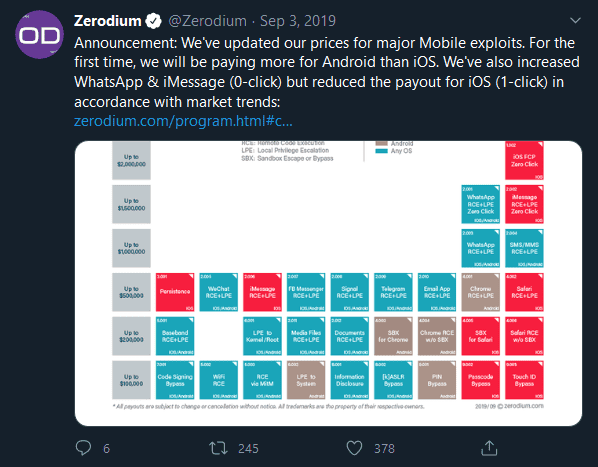
Apple and iPhone retained the title of most-expensive to exploit consistently for the next several years, so it may come as a surprise to some that Apple has been falling behind in the arms race. In September of 2019, Forbes noted that bounties for iOS had fallen behind Android bounties by upwards of $1 Million US.
Now the trend is accelerating. In September 2019, Zerodium made a splash in cybersecurity news when they announced that they would no longer be accepting submissions for iOS and Safari vulnerabilities. So what can we infer from Apple’s fall from the top?
Monoculture can be a security risk
A uniform product creates a uniform threat model. If one iOS device can be exploited, any iOS device can be exploited. This actually creates an incentive for exploit developers to target iOS by ensuring that the broadest user-base is always affected by a zero-day. They get the most bang for their buck.
Many hands make light work. While Apple does make use of freelancers and bounty-hunters in their development ecosystem, the barriers to entry are much higher than Android. This means that it is less likely someone with a solution has access to apply that solution.
While some would lay the blame for this on Apple, we would like to suggest that it is the strength of the Android security community which is to be commended. While Apple’s Security team works alone to resolve vulnerabilities, Android can rely on not only the great team at Google Security, but also on the community of developers and corporate partners up-streaming patches monthly, and in their own direct interests.
Has Android Security caught up to its competitors?
Google announced in late 2019 that it would provide up to $1M for an exploit of the Titan M security module present in Pixel 3 devices and later. This move begins to equalize the profit potential for exploit developers and forces them to make an important decision. Should the exploit developer contribute to zero-day programs for malicious use? Or should they capture the bug bounty, further securing Android for the benefit of all? Consider that 5 years ago Android was widely recognized as behind iOS in security and privacy controls. Compare that to the current state of available Android offerings. In addition, Zerodium increased the bug bounty for Android exploits to $2.5M, up from $1M and surpassing the iOS bug bounty. The price imbalance is telling if the companies devoted to hacking platforms are willing to pay 200% more to target Android.
Whether Android is now more secure than iOS is still up for debate. However, it cannot be denied that Android’s security is rapidly catching up. Secure Android provides best-in-class security for any organization.
Avoid the monoculture and data-centralization of other platforms. Use mainstream secure hardware and add CopperheadOS for maximum protection.
